Mardi, 26 décembre 2017
Traduction: [ Google | Babelfish ]
Catégories : [ TV/Cinéma ]

Wikipedia
As a child, Riley's (personified) emotions are dominated by Joy, who does her
best to remain on top of things. But when, at age 11, she moves with her
parents from Minnesota to San Francisco, she starts to feel homesick and
depressed. In her mind, this translates as Sadness taking control more often,
and eventually to accidentaly sending happy core memories to the maze-like
long-term memory. Joy and Sadness attempt to recover them, but transformations
in Riley's personality (and especially her decision to run away back to
Minnesota) makes going back to their headquarter very difficult. On the way
they meet Riley's childhood's imaginary friend who shows them the path to a
station for the Train of Thoughts. After many setbacks, Joy and Sadness return
to the headquarters that was manned only by Anger, Disgust and Fear, and only
Sadness is able to get Riley to change her mind and retuns home.
[ Posté le 26 décembre 2017 à 23:45 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/TV/Cinema/inside_out.trackback
Commentaires
Aucun commentaire
Traduction: [ Google | Babelfish ]
Catégories : [ TV/Cinéma/Marvel ]

Wikipedia
A terrorist named the Mandarin has attackd several targets in the USA. When
one of Tony Stark's friend is killed, Stark starts to investigate and
discovers that the latest attack is due to people who have been genetically
modified to acquire super strength and recover from injuries, with the
drawback that they heat up and explode from time to time. The Mandarin then
attacks Stark's home, and Stark escapes in the nick of time in an experimental
Iron Man suit. His investigation leads him to finding the lair of the
Mandarin, who is only an actor manipulated by Killian, a mad scientist who had
invented the genetic treatment. Killian's plan is to kill the President aboard
Air Force One, but all the passenger of the plane are saved by Stark. Only the
president is still missing, abducted by Killian. Stark eventually saves the
president and kills Killian.
[ Posté le 26 décembre 2017 à 23:45 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/TV/Cinema/Marvel/iron_man_3.trackback
Commentaires
Aucun commentaire
Samedi, 16 décembre 2017
Traduction: [ Google ]
Catégories : [ TV/Cinéma ]
Wikipedia
[ Posté le 16 décembre 2017 à 23:45 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/TV/Cinema/ella_ja_kaverit.trackback
Commentaires
Aucun commentaire
Dimanche, 12 novembre 2017
Traduction: [ Google | Babelfish ]
Catégories : [ Bière/Tempest Brewing ]

“zesty citrus… Golden Promise, Munich and Cara malts, North American
hops… soft fruit, biscuit malt, citrus and tropical flavours”
Just another ale, quite nice. Contains wheat, barley and oats.
Tempest Brewing Co Ltd, Tweedbank, Scottish Borders, Scotland. 3.8% alcohol.
[ Posté le 12 novembre 2017 à 22:38 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Tempest_Brewing/tempest_brewing_the_pale_armadillo.trackback
Commentaires
Aucun commentaire
Dimanche, 5 novembre 2017
Traduction: [ Google ]
Catégories : [ Bière/Hiisi ]

“hedelmäinen passiosessio”
Hedelmäinen, vähän kirpeä. Se ei ole minun suosikki. Sisäältää ohramallasta,
vehnämallasta, kauraa, passionhedelmää.
Panimoyhtiö Hiisi, Jyväskylä, Suomi. 4.4% alkoholia.
[ Posté le 5 novembre 2017 à 23:10 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Hiisi/hiisi_hattara.trackback
Commentaires
Aucun commentaire
Samedi, 28 octobre 2017
Traduction: [ Google | Babelfish ]
Catégories : [ Bière/Tiny Rebel ]

Just another ale, quit bitter. Contains malted barley and malted wheat.
Tiny Rebel Brewing Co., Newport, Wales. 4.5% alcohol.
[ Posté le 28 octobre 2017 à 18:42 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Tiny_Rebel/tiny_rebel_beat_box.trackback
Commentaires
Aucun commentaire
Dimanche, 22 octobre 2017
Traduction: [ Google ]
Catégories : [ Bière/Hiisi ]

“hedelmainen, kukkaisa”
Hedelmäinen ja kukkaisa, niin kun sanottu. Aika hyvää. Sisältää ohramallasta
ja vehnämallasta.
Panimoyhtö Hiisi, Jyväskylä, Suomi. 5.4% alkoholia.
[ Posté le 22 octobre 2017 à 10:58 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Hiisi/hiisi_hati.trackback
Commentaires
Aucun commentaire
Mercredi, 18 octobre 2017
Traduction: [ Google | Babelfish ]
Catégories : [ TV/Cinéma ]
Wikipedia
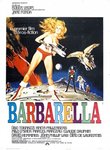
Barbarella is sent by the president of Earth to Tau Ceti, to find the
scientist Durand Durand and recover the terrible weapon he invented. After a
couple of crash landings and improbable rescues, she arrives at the labyrinth
where she learns than Durand Durand is in the city of Sogo. She is flown there
by Pygar, the last of the bird-people. They are both taken prisoner by the
Black Queen and her Concierge, but Barbarella is rescued by the leader of the
underground. She is then again taken prisoner by the Concierge, who happens to
be Durand Durand. He then locks up Barbarella with the Queen, and crowns
himself king. But the people from the labyrinth revolt using weapons found in
Barbarella's ship, while the Queen releases the Matmos (a liquid creature
leving below the city that provides the city with energy, in exchange for the
evilness of condemned people thrown into it), thus destroying the city. Pygar,
whom the Queen had kept as a pet, saves both Barbarella and the Queen.
[ Posté le 18 octobre 2017 à 23:16 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/TV/Cinema/barbarella.trackback
Commentaires
Aucun commentaire
Mardi, 17 octobre 2017
Traduction: [ Google | Babelfish ]
Catégories : [ TV/Cinéma ]
Wikipedia
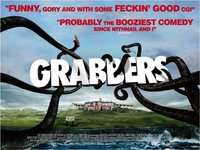
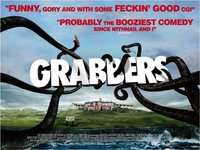
An alien object falls into the sea not far from an island off the coast of
Ireland. Soon after people disappear, and a local fisherman catches a strange
creature. The octopus-like creature attacks the man, but he manages to get rid
of it and kill it. Along with the local police, O'Shea, a drunk resident male officer
and Nolan, an enthousiastic female officer, the local doctor and marine biologist
study the creature and discover that it needs water and lives on blood, but is
allergic to alcohol (that's why the constantly drunk fisherman survived the
attack). Since the creature has laid an egg, there must be a male around; the
lair of the gigantic male is soon discovered. Since a storm is coming and no
help can be expected, they convince all the inhabitants to get drunk all
together the same evening at the local pub. The pub is first attacked by the
hatchlings which are quickly killed by the fire caused by a drunk Nolan. To
allow the people to evacute the pub safely, O'Shea and Nolan attract the male
creature to a recycling plant where they kill it by setting it to fire.
[ Posté le 17 octobre 2017 à 23:45 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/TV/Cinema/grabbers.trackback
Commentaires
Aucun commentaire
Vendredi, 13 octobre 2017
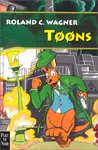
Catégories : [ Livres/RC Wagner ]
© Amazon.fr
Tem est engagé par un collectionneur de livres de science-fiction pour
retrouver le voleur du Faisceau chromatique, un livre écrit par le
grand-père de Tem décrivant un voyage dans des univers parallèles. Tem
découvre que tous les exemplaires du livre ont été volés, et les traces de
peinture chez le collectionneur ainsi que le fait que de plus en plus de gens
rapportent avoir vu des personnages de dessin animé dans les rues de Paris le
forcent à conclure que le voleur est bien un toon, probablement issu de la
Psychosphère. Durant l'enquête, Ramirez est attiré dans une banlieue perdue
vers une maison moitié réelle en trois dimensions, moitié dessinée en deux
dimensions, que l'entraîne vers l'univers des toons, où il lui arrive une série
de mésaventures improbables. Pour aider Tem à en apprendre davantage sur le
Faisceau chromatique, Eileen fouille l'appartement du défunt grand-père.
Elle y observe un homme voler un objet dissimulé dans un placard secret, et
réussit à le suivre et à faire savoir à Tem où il se trouve. Tem fouille
l'appartement du voleur et se fait prendre par ce dernier, qui n'est autre
qu'un des clone, travaillant pour la Nakimeraï, pouvant servir de réceptacle
aux Yeux-Rouges, l'archétype ennemi de Tem. Le clone emmène Tem de force à la
maison servant de passage vers l'univers des Toons. Tem y retrouve
Ramirez, qui y a retrouvé le kangourou voleur des livres. Menacés de mort par
le clone, ils sont sauvés par l'apparition inopinée de Gloria. Lorsque le
kangourou annonce que les livres sont stockés dans sa poche, Gloria y plonge
pour vérifier, et tombe dans le piège qui avait été tendu à son intention (par
les Yeux-Rouges?) depuis le début ; elle disparaît sans laisser de trace.
[ Posté le 13 octobre 2017 à 23:45 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/RC_Wagner/toons.trackback
Commentaires
Aucun commentaire
Dimanche, 8 octobre 2017
Traduction: [ Google | Babelfish ]
Catégories : [ TV/Cinéma ]

Wikipedia
At the dawn of mankind, a black monolith appears and teaches the protohumans
te use tools. In 2001, a similar monolith is found on the Moon, emitting a
signal towards Jupiter. Eighteen months later, a mission is nearing Jupiter,
under the control of a supercomputer. The computer decides the two human
astronauts are going to jeopardize his mission, and attempts to kill them
during EVAs. The second astronaut manages to return to the ship and disables
the computer. He finally reaches the monolith near Jupiter, enters it, sees
psychedelic lights, sees himself grow old, die and be reborn.
[ Posté le 8 octobre 2017 à 17:53 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/TV/Cinema/2001_a_space_odyssey.trackback
Commentaires
Aucun commentaire
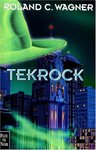
Catégories : [ Livres/RC Wagner ]
© Amazon.fr
Tem part à la recherche de l'identité d'un homme dont les premiers souvenirs
remontent à la fin de la Terreur. Il découvre que l'homme a été vu en
compagnie d'une bande de motards, dont le visage de l'un d'entre eux est
tatoué d'un crâne, et un autre a passé des jours en orbite sur sa moto, aux
débuts de la Terreur. Tem pense à juste titre que ces personnages sont des
Archétypes qui étaient présents dans la réalité consensuelle lors de la
Terreur, et a peur que son éternel adversaire aux yeux rouges soit mêlé à
cette histoire. Au cours de son enquête, Tem découvre que son client, qui a été
enlevé par des cyberninjas, collectionne les disques de rock'n roll et autres
souvenirs liés à cette musique. Il finit par déduire que son client n'est
autre le l'archétype du Rock'n Roll, resté malgré lui dans la Réalité à la fin
de la Terreur.
[ Posté le 8 octobre 2017 à 12:07 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/RC_Wagner/tekrock.trackback
Commentaires
Aucun commentaire
Traduction: [ Google ]
Catégories : [ Bière/Hiisi ]

“Valdelmalla ja passionhedelmällä maustettu”
Aika kirpeä, maistuu vadelmalla. Sisältää ohramallasta ja vehnämallasta.
Panimoyhtiö Hiisi, Jyväskylä, Suomi. 4.5% alkoholia.
[ Posté le 8 octobre 2017 à 11:48 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Hiisi/hiisi_gosebump.trackback
Commentaires
Aucun commentaire
Dimanche, 1er octobre 2017
Traduction: [ Google | Babelfish ]
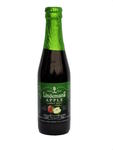
Catégories : [ Bière/Lindemans ]
“one-year-old oak-aged lambic and apple juice… sweet of red apple…
freshness of green apple… sour of a lambic beer”
Very sweet, tastes of apple, with a recognizable sour lambic aftertaste.
Contains barley malt and wheat.
Lindemans, Vlezenbeek, Belgium. 3.5% alcohol.
[ Posté le 1er octobre 2017 à 11:21 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Lindemans/lindemans_apple.trackback
Commentaires
Aucun commentaire
Dimanche, 24 septembre 2017
Catégories : [ Livres/RC Wagner ]
© Amazon.fr
Tem est engagé par le président d'une des huit technotrans pour enquêter sur
les morts suspectes des membres d'un groupe de musique à la mode. Ces
personnes sont connues pour abuser des psychotropes, et leurs morts ne sont
pas forcément suspectes. La transparence de Tem s'intensifie, au point
qu'Eileen, interrogeant à sa place les suspects, oublie son existence et
l'enquête. Seul Ramirez se souvient de lui et lui permet de continuer à
enquêter, le conduisant à rencontrer un informateur. Ce dernier révèle que le
tueur est un changeforme venant d'un univers parallèle
parmi les huit qui ont été conditionnés par le gourou d'une secte, puis
revendus à chacune des technotrans, dont un membre a été imprégné pour
contrôler le tueur. Un des tueurs a été assigné à une personne capable d'être
possédé par l'Archétype du mal
qui a accidentellement été invoqué par les musiciens lors d'une datura-party.
Pour cacher son existence, l'Archétype a utilisé le tueur pour éliminer les
personnes présentes à la fête, et a tué d'autres musiciens pour cacher les
relations entre ces assassinats.
[ Posté le 24 septembre 2017 à 20:53 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/RC_Wagner/l_aube_incertaine.trackback
Commentaires
Aucun commentaire
Catégories : [ Livres/RC Wagner ]
© Amazon.fr
Tem est accusé du meurtre de Viard, un psychologue à qui il venait rendre
visite dans son laboratoire. Il est innocenté, mais peu après, il est à
nouveau accusé du meurtre d'un collègue de Viard, et cette fois-ci les preuves
sont suffisantes pour que l'inspecteur Trovallec le mette en détention. Tem
s'évade avec l'aide de Gloria, et part se réfugier chez ses parents à
Pouvroux, car Trovallec semble annuler le Talent de transparence de Tem, ce
qui rend sa cavale difficile. Trovallec arrête alors Eileen pour complicité,
et Tem rentre à Paris pour la faire évader tandis que des amis entraînent
l'inspecteur loin de la capitale afin que le détective puisse à nouveau
profiter de sa Transparence. Tem apprend alors que Viard et son grand-père se
connaissaient, et que ces derniers mentionnent que durant la Grande Terreur
Primitive, un Archétype représentant le Mal absolu datant de l'aube de
l'humanité a été expulsé de la Psychosphère. Cet Archétype a pris le contrôle
de Trovallec et a assassiné les deux scientifiques qui étaient sur le point de
découvrir son existence. L'absence de l'Archétype de la Psychosphère explique
aussi que l'humanité soit devenue moins violente après la Terreur. Sur le
point d'être pris, l'Archétype s'enfuit de corps de Trovallec, et Tem est
innocenté.
[ Posté le 24 septembre 2017 à 20:49 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/RC_Wagner/l_odyssee_de_l_espece.trackback
Commentaires
Aucun commentaire
Dimanche, 17 septembre 2017
Catégories : [ TV/Cinéma ]

Allocine.fr
Lors de la visite d'un chenil de la SPA, Boule devient le maître d'un cocker,
nommé Bill. Ce dernier causant trop de catastrophes, le père de Boule décide
de l'abandonner lorsque son travail le pousse à déménager en banlieue
parisienne. Bill parvient cependant à suivre la famille, qui manque d'écraser
une tortue en cours de route. Cette dernière, Caroline, est alors adoptée, et
Bill et elle tombent immédiatement amoureux. À Paris, Bill est laissé seul
dans l'appartement, cause à nouveau des catastrophe, notamment quand Bill
lance Caroline dans le vide-ordure et Boule met accidentellement le feu aux
poubelles en la recherchant. Lorsque Boule entend ses parents parler de donner
Bill, il fugue avec son chien et se cache dans le local des poubelles. Bill
est accidentellement emmené par le camion des poubelles à la décharge, et
toute la famille part à sa poursuite pour sauver le chien de l'incinération.
Le père de Boule démissionne et invente les personnages de bande dessinée
inspirées de son fils et de son chien. La famille redéménage dans une maison
individuelle, et Boule rencontre Pouf, un voisin.
[ Posté le 17 septembre 2017 à 11:16 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/TV/Cinema/boule_et_bill.trackback
Commentaires
Aucun commentaire
Samedi, 9 septembre 2017
Catégories : [ Livres/RC Wagner ]
© Amazon.fr
Tem est engagé pour retrouver une jeune femme embrigadée dans une secte, dont
de gourou a la réputation de laver les cerveaux de ses disciples. Tem
s'introduit de nuit dans les locaux de la secte, et découvre que les membres
se cachent dans les souterrains et se livret à des activité étranges, par
exemple « décopier » un livre en enlevant l'encre des pages à la plume.
Assistant à une cérémonie, il est mentalement découvert par le gourou et
échappe de peu au lavage de cerveau. Il s'enfuit dans les souterrains au
moment où ceux-ci sont attaqués par des agents étrangers. Tem est endormi et
et se réveille dans un monde parallèle, où l'URSS a envahi le monde. Il
rencontre le petit ami de la jeune femme, qui se fait passer pour le chef des
rebelles. Avec l'aide de ces derniers, Tem retrouve la jeune femme dans les
locaux du KGB, et tous trois s'échappent avec l'aide de Gloria, l'aya amie de
Tem, qui le suivait discrètememt. De retour dans leur monde d'origine, Tem
affronte le gourou et parvient à le mettre hors d'état de nuire. Tem suppose
que le gourou a concentré le lien à la Psychosphère de ses disciples pour
créer le passage, mais il s'avère que ce dernier est très ancien, et des
créatures interdimensionnelles, les Ravisseurs quantiques, travaillent à les
refermer.
[ Posté le 9 septembre 2017 à 15:32 |
1
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/RC_Wagner/les_ravisseurs_quantiques.trackback
Commentaires
L'aube incertaine
Commentaire N° 1, Blog & White
le 24 septembre 2017 à 20:52
Dimanche, 3 septembre 2017
Traduction: [ Google ]
Catégories : [ Bière/Hiisi ]

“Cascade ja Mandarina Bavaria -humalat… sitruksinen aromi”
Kukkanen ja hedelmäinen maku; ei mitään erikoista. Sisältää ohramallasta ja
vehnämallasta.
Panimoyhtiö Hiisi, Jyväskylä, Suomi. 4.4% alkoholia.
[ Posté le 3 septembre 2017 à 22:49 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Hiisi/hiisi_red_wheat_ale_harjun_kettu.trackback
Commentaires
Aucun commentaire
Vendredi, 1er septembre 2017
Catégories : [ Livres/RC Wagner ]
© Amazon.fr
Tem est engagé pour résoudre le meurtre en chambre close d'un physicien, tué
par balle dans un hôtel faisant face à son institut de recherche. Le fait est
d'autant plus remarquable que la victime possède le Talent d'être aimé de
toute le monde, ce qui rend toute violence à son encontre très imporbable. Tem
retrouve ensuite pendu le collègue de la victime qui voulait lui faire des
confidences. Sur cette deuxième victime, Tem trouve un pendentif qu'il demande
à un ami libraire d'identifier. Le libraire est retrouvé mort à son tour.
Voulant interroger le collègue de la première victime, qui a hérité de son
post de directeur de recherche, il retrouve ce dernier mourant dans son
bureau, tué lui aussi par balle un instant avant l'arrivée du détectve. Peu
après, Tem se rend compte qu'on l'a drogué au Désincarn, drogue qui pousse
couramment au suicide les personnes normales (ce que Tem n'est pas) et en
conclue que c'est ainsi que la deuxième victime a été tuée. Grâce à son ami
Ramirez il apprend l'origine du pendentif, qui relie les scientifiques
assassinés et leur dernier collègue survivant ; ensemble ils travaillaient
sure un système de transport spatial, qui est essentiellement une forme de
téléportation par trou de ver. Tem piège l'assassin en l'incitant à utiliser
la même méthode sur lui (protégé d'un gilet pare-balles).
[ Posté le 1er septembre 2017 à 18:10 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/RC_Wagner/la_balle_du_neant.trackback
Commentaires
Aucun commentaire
Dimanche, 27 août 2017
Traduction: [ Google | Babelfish ]
Catégories : [ Bière/The Wild Beer Company ]

“tropical aromas… tropical and citrus fruits”
Very fruity, as advertised. Contains barley malt and wheat.
The Wild Beer Co., Shepton Mallet, Somerset, England. 6.8% alcohol.
[ Posté le 27 août 2017 à 20:29 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/The_Wild_Beer_Company/wild_beer_company_madness.trackback
Commentaires
Aucun commentaire
Dimanche, 20 août 2017
Traduction: [ Google | Babelfish ]
Catégories : [ Livres/Discworld ]
© Amazon.fr
On Granny Weatherwax's death, Tiffany Aching inherits her cottage. She starts
to work both on the Chalk and in Lancre, having too little time for the people
of both places. In the meanwhile, the queen of elves is kicked out of her
kingdom by a rebellious faction onto the land of humans; those elves do not
believe that the world is changing and that the rapidly increasing usage of
iron (e.g., the railroad) makes it unhealthy for them. After Granny's death,
the gates between the two worlds are easier to go through, and some elves long
for the good old day when they could freely enjoy doing mischief among humans.
Tiffany finds and tends to the ex-queen's wounds, and bit by bit teaches her
what it means to be humane, hoping she would eventually make the elves
sympathetic to the humans. Tiffany also accepts Geoffrey as an apprentice; the
young man is able to calm people and make them more reasonable. He has as a
pet a goat named Mephistopheles, who can count and use the privy. When the
elves get ready to invade the Disc, Tiffany leads the witches of the Chalk to
fight them, while Nanny leads the witches of Lancre and Geoffrey organizes the
old gentlemen of the country. The elves are defeated, their queen is killed in
the battle, and Tiffany somehow manages to make the passage between the two
worlds much harder than it has ever been. In the end, Geoffrey receives
Granny's cottage and becomes a witch of Lancre.
[ Posté le 20 août 2017 à 23:17 |
1
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/Discworld/the_shepherd_s_crown.trackback
Commentaires
Traduction: [ Google | Babelfish ]
Catégories : [ Bière/Brewdog ]

“crushed coffee beans, cocoa nibs and dark malts… infusions of toasted oak
chips”
Strong and sweet, clear coffee aroma and hints of cocoa. Contains malted
barley and wheat.
BrewDog Ltd., Elton, Scotland. 10.0% alcohol
[ Posté le 20 août 2017 à 21:04 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Brewdog/brewdog_cocoa_psycho.trackback
Commentaires
Aucun commentaire
Dimanche, 13 août 2017
Traduction: [ Google | Babelfish ]
Catégories : [ TV/Cinéma ]

Wikipedia
Paleontologist are invited to give their approval of a theme park, built on an
isolated island, featuring real dinosaurs, genetically reconstructed from DNA
found in jurassic mosquitos preserved in amber. During the tour of the park,
the main IT engineer runs a program that disables safety measures so that he
can steal embryos and resell them. At the same time, a storm arrives on the
island, and the engineer, lost in the park, gets killed by a carnivorous
dinosaur. More dinosaurs get loose as the electric fences are unoperative. The
humans, blocked in the middle of the tour, manage to escape the tyrannosaurus
and spend the night in a tree. Meanwhile, other people attempt to reboot the
whole computer system and restart the power plant to be able to call for help,
while escaping velociraptors. In the end, the surviving characters escape the
island by helicopter.
[ Posté le 13 août 2017 à 12:33 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/TV/Cinema/jurassic_park.trackback
Commentaires
Aucun commentaire
Traduction: [ Google | Babelfish ]
Catégories : [ Bière/Stone's ]
Very sweet ginger beer, quite nice if you don't mind the sweetness.
Produced for Accolate Wines Ltd, Guildford, London, England. 4.0% alcohol.
[ Posté le 13 août 2017 à 12:00 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Stone_s/stone_s_ginger_joe_limited_edition.trackback
Commentaires
Aucun commentaire
Vendredi, 4 août 2017
Catégories : [ Livres/Le Paris des merveilles ]

© Amazon.fr
Quelques mois après le événements de L'élixir
d'oubli,
Isabel manque de sauver un elfe noir porteur d'un étrange tatouage. Peu après,
Troisville demande à son ami Griffont d'être un témoin lors de son duel avec
le mage Incarnat Dalmas. Mais Dalmas disparaît mystérieusement la nuit avant
le duel, et Troisville est accusé de l'avoir tué. En même temps, le Silas, un
groupe terroriste de l'époque de la guerre entre fées et dragons, fait
exploser une bombe sous la tour Eiffel, manquant de tuer Isabel et Cécile de
Brescieux qui voulait faire des révélations à cette dernière à propos de
Dalmas. De plus, un vieil elfe, ami d'Isabel, est enlevé par le Silas alors
qu'il allait lui aussi lui faire des révélations. Dans l'espoir de le
protéger, Griffont et Isabel emmènent Troisville dans une maison connue d'eux
seuls, mais ils sont retrouvé par des créatures de la Reine Noire et
Troisville est tué. Griffont apprend alors qu'Adélaïde, la fille de son ami le
maître d'armes Mortaigne, à qui Troisville était fiancé, est en fait la fille
de Sélène, amie d'Isabel et sœur de la reine Méliane, qui est morte de chagrin
après avoir été abandonnée par Jeanson, un homme qui l'avait séduite par jeu.
Mortaigne et Jeanson étaient amis par le passé. Jeanson avait ensuite fui en
Russie pour faire des recherches interdites sur la transformation du corps, et
revenu sous les traits de Dalmas. La police et Griffont retrouvent ensuite la
trace du Silas dans une ferme isolée, qui est prise d'assaut. Griffont et
Isabel y découvrent que la Reine Noire, qui prépare un attentat à l'ambassade
d'Ambremer à Paris lors d'une cérémonie officielle. Isabel défait la Reine
Noire et sauve Adélaïde que la Reine Noire, se faisant passer pour son amie,
avait poussée au suicide.
[ Posté le 4 août 2017 à 22:25 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/Le_Paris_des_merveilles/le_royaume_immobile.trackback
Commentaires
Aucun commentaire
Traduction: [ Google ]
Catégories : [ Bière/Hiisi ]
“mineraalinen ja kevyen sitruksinen… greipinkuori”
Sitruksinen, maistuu vähän greipiltä. Sisältää ohramallasta ja vehnämallasta.
Panimoyhtiö Hiisi, Jyväskylä, Suomi. 2.8% alkoholia.
[ Posté le 4 août 2017 à 21:31 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Hiisi/hiisi_lempo.trackback
Commentaires
Aucun commentaire
Mercredi, 2 août 2017
Traduction: [ Google | Babelfish ]
Catégories : [ TV/Cinéma ]

Wikipedia
The planet Mül is destroyed as a collateral damage of a war between humans and
some other alien species. Thirty years later, only a few survivors, named
Pearls, remain. Records indicate that the planet was uninhabited. Valerian and
Laureline are tasked to recover the last of the Mül convterters from a black
market dealer, unknowingly taking it away from the Pearls who were about to
buy it. Commander Filitt plans to give the converter as a gift during a
meeting of the council of Alpha, a huge complex of ships and space stations
where thousands of alien species cohabitate. The Pearls attack the conference
and kidnapp Filitt, but fail to notice that Laureline, as Filitt's bodyguard,
was holding onto the converter. Valerian chases the Pearls through Alpha, but
Laureline loses contact with him as he enters a radioactive zone at the center
of the complex, zone that had appeared recently, grows, and from which no-one
has ever come back. Laureline manages to locate Valerian, but she is kidnapped
by a primitive species and about to be eaten by their emporor when she is
saved by Valerian, who had enrolled Bubble, a shapeshifter, to disguise him as
a one of the primitives. Bubble dies in the fight, and Valerian and Laureline
eventually reach the Pearl's hideout. They learn the fate of Mül and Filitt's
involvement and ensuing coverup. While Filitt's robotic troops prepare to
attack the Pearls, Valerian accepts to give them the converter, allowing
them to produce enough energy to power the ship they had been secretly
constructing and escape in the nick of time.
[ Posté le 2 août 2017 à 23:45 |
1
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/TV/Cinema/valerian_and_the_city_of_a_thousand_planets.trackback
Commentaires
Mardi, 25 juillet 2017
Catégories : [ Livres/Le Paris des merveilles ]

© Amazon.fr
Quelques mois après les événements des Enchantements
d'Ambremer,
Griffont est chargé d'enquêter sur un cas d'empoisonnement impliquant la
magie noire. Tixier, gendre de la victime avait été chargé d'obtenir tous les
exemplaires de l'Athanor lumineux, dans l'espoir que l'un des volumes se
révèle être l'Athanor ténébreux, dont l'encre avait été mêlée aux cendres de
Levrat, un dragon brûlé sur le bucher en 1720, époque à laqelle Griffont
rencontre Isabel, et déjoue un complot mené Levrat pour soumettre le Régent à
sa volonté et ainsi prendre le pouvoir dans l'ombre. Nero se révèle être un
dragon, autrefois gouverneur d'une cité rebelle à Ambremer, qui a tenté de
porter la guerre entre fées et dragons sur Terre pour ne pas être obligé de se
soumettre à ces dernières. Son plan consistait à permettant à son frère d'être
condamné au bucher tout en buvant l'Élixir d'oubli, ce qui permettrait à ce
dernier de contourner l'Interdit qui force les dragons à prendre forme humaine
sur Terre. Ce plan avait été déjoué par Merlin, et Levrat avait été banni au
moment de périr sur le bûcher. Sa résurrection en 1909 par Nero, juste avant
que Griffont ne tue ce dernier, donne vie à un dragon spectral dont Isabel se
débarasse en le faisant passer par un passage menant à Ambremer.
[ Posté le 25 juillet 2017 à 23:45 |
1
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/Le_Paris_des_merveilles/l_elixir_d_oubli.trackback
Commentaires
Le royaume immobile
Commentaire N° 1, Blog & White
le 4 août 2017 à 22:25
Dimanche, 23 juillet 2017
Traduction: [ Google | Babelfish ]
Catégories : [ Bière/Little Valley ]

A bit sour with a hint of cherry. Quite pink beer, too. Contains barley malt.
Little Valley Brewery, Hebden Bridge, West Yorkshire, England. 4.5% alcohol.
[ Posté le 23 juillet 2017 à 11:47 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Little_Valley/little_valley_cherry_popper.trackback
Commentaires
Aucun commentaire
Dimanche, 16 juillet 2017
Catégories : [ Livres/Enola Holmes ]
© Amazon.fr
Enola est la petite sœur de Sherlock Holmes. Lorsque sa mère disparaît sans
explication le jour de son treizième anniversaire et que son frère aîné
Mycroft veut l'envoyer dans une école pour jeune filles, elle se déguise en
veuve et s'enfuit de la maison familiale pour Londres. En chemin, elle enquête
sur la disparition du jeune Lord Tewksbury et déduit qu'il a fui sa mère trop
protectrice et est parti chercher l'aventure à Londres, probablement sur un
vapeur en partance pour l'Amérique. À Londres, Enola se perd dans l'East End
et est kidnappée par ceux qui ont aussi kidnappé Tewksbury. Les deux enfants
parviennent à s'enfuir et Enola convainc le garçon de se présenter à Scotland
Yard. Enola parvient à communique avec sa mère par l'entremise de petites
annonces et d'un code secret décrit dans un livre reçu de sa mère pour son
anniversaire. Elle réussit finalement à s'installer à Londres comme secrétaire
d'un détective fictif, au nez et à la barbe de ses frères.
[ Posté le 16 juillet 2017 à 23:45 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/Enola_Holmes/la_double_disparition.trackback
Commentaires
Aucun commentaire
Samedi, 8 juillet 2017
Traduction: [ Google ]
Catégories : [ Bière/Hiisi ]

“sitruksinen… Mosaic-humala”
Panimoyhtiö Hiisi, Jyväskylä, Suomi. 4.4% alkoholia.
[ Posté le 8 juillet 2017 à 23:45 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Hiisi/hiisi_peri.trackback
Commentaires
Aucun commentaire
Jeudi, 6 juillet 2017
Catégories : [ Livres ]
Une planète lointaine a été colonisée par des humains qui ont développé une
technologie permettant la réincarnation dans de nouveaux corps, et des
pouvoirs permettant à certains élus de se prendre pour les dieux du panthéon
hindou, et de vivre retirés dans une cité céleste, tout en empêchant le peuple
d'évoluer en sciences et technologie. L'un des dieux décide de revenir sur
terre et de prêcher une autre spiritualité et se fait appeler Bouddha. Il
décide de libérer les habitants originels de la planète, des « démons » qui
avaient été faits prisonniers lors de la colonisation afin de l'aider à
renverser le pouvoir des autres dieux et de donner aux hommes normaux le
contrôle de la technologie de réincarnation, tuant définitivement au passage
la plupart des dieux et permettant aux hommes de recommencer à développer les
sciences et la technologie sans entraves de la part des dieux.
[ Posté le 6 juillet 2017 à 23:45 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/seigneur_de_lumiere.trackback
Commentaires
Aucun commentaire
Mercredi, 28 juin 2017
Catégories : [ Livres/BD/Yoko Tsuno ]
© Amazon.fr
Yoko et Émilia sont attirées par Lâthy dans une base secrète de Vinéens en
Écosse. Elles y découvrent un peuple Celte vivant sous terre. Zarkâ y a trouvé
refuge et c'est elle qui a besoin de l'aide de Yoko afin de protéger le peuple
d'un homme se prenant pour Merlin l'enchanteur vivant dans un monastère
entouré de moines et de moine-robots. Il prétend qu'Iseut, une jeune femme
celte, sera le réceptacle de la réincarnation de la fée Viviane. Merlin est
tué accidentellement alors qu'il tentait de s'en prendre à Iseut, et on
découvre qu'il était en partie robotisé. Yoko explore ensuite un ordinateur
renfermant une intelligence artificielle qui veille sur les celtes et dont
l'arrivée des vinéens a bouleversé les plans de faire d'Iseut la reine du
peuple et de les guider vers la grotte interdite où ils pourront s'établir.
Yoko se charge alors de mettre en œuvre le plan de l'IA.
[ Posté le 28 juin 2017 à 14:19 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/BD/Yoko_Tsuno/le_temple_des_immortels.trackback
Commentaires
Aucun commentaire
Catégories : [ Livres/BD/Midi minuit ]
© Amazon.fr
Des écrivains et critiques littéraire sont assassinés par des injections
d'encre mélangée de poison. Beltram et Marnie enquêtent, tandis que Jim et
Jenna sont pris en charge par des médecins qui tentent de séparer leurs deux
corps mélés. Leurs essais sont infructueux, et le Commandeur passe alors un accord
avec l'Invisible et Dwaine qui réussissent effectivement à permettre à Jim de
se changer en Jenna et vice-versa, mais profitent de l'occasion pour s'évader,
puis assassiner le Commandeur. De leur coté, Beltram et Marnie déduisent des
meutres que l'assassin est un écrivain talentueux mais oublié qui se venge en
empoisonnant ses victimes avec un médicament qu'utilise sa femme, infirmière.
[ Posté le 28 juin 2017 à 13:52 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/BD/Midi_minuit/l_affaire_de_la_pieuvre.trackback
Commentaires
Aucun commentaire
Catégories : [ Livres ]
© Amazon.fr
Bien qu'à la retraite, Holmes est envoyé par le Foreign Office en Alsace en
1909 pour découvrir quel secret se cache au Haut-Kœnigsbourg depuis le temps
des croisades; selon la rumeur, ce secret est convoité par l'empereur
Guillaume II et censé apporter un avantage militaire considérable. Sous
couvert d'étudier les châteaux restaurés, ils arrivent à Sélestat où un agent
français leur apprend que lors de la restauration du château en 1902, trois
ouvriers sont morts mystérieusement, indiquant qu'on s'est débarrassé des
témoins ayant découvert ledit secret, le chantier de restauration du château
n'étant qu'un prétexte pour entreprendre des fouilles archéologiques. Les
chambres d'hôtel de Holmes et Watson sont ensuite fouillées par des
séminaristes catholiques, indiquant que le Vatican s'intéresse au secret en
question. Aidé par un chanoine du Mont Sainte-Odile, Holmes en déduit qu'il
doit s'agir de la Sainte-Lance, qu'un soldat romain a utilisé pour percer le
flanc du Christ. Grâce à la fouille par Watson de la chambre d'hôtel d'une
historienne et espionne de Guillaume II, ils découvrent que la relique était
cachée dans l'Oedenbourg, le château voisin surnommé le Petit
Haut-Kœnigsbourg. La relique a été déplacée par la suite dans le château une
fois restauré. Holmes et Watson parviennent à s'emparer de la relique et à la
rapporter en Grande-Bretagne.
[ Posté le 28 juin 2017 à 13:02 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/sherlock_holmes_et_le_mystere_du_haut-koenigsbourg.trackback
Commentaires
Aucun commentaire
Vendredi, 23 juin 2017
Catégories : [ Livres ]
© Amazon.fr
Transcription d'un discours d'Umberto Eco, où il décrit les caractéristiques
de l'archétype du fascisme:
- culte de la tradition, même si le syncrétisme de plusieurs traditions
conduit à des contradictions
- refus du modernisme
- irrationalisme
- culte de l'action pour l'action, la réflexion et la culture sont suspects
- refus de la critique, qui est pourtant à la base du progrès des sciences: le
désaccord est un trahison
- exacerbation de la peur de la différence
- appel aux classes moyennes frustrées, épouvantées par la pression des
classes sociales inférieures
- à ceux qui n'ont pas d'identité sociale, on dit qu'ils ont au moins le
privilège d'être nés dans le même pays, c'est le nationalisme
- les ennemis sont les seuls à pouvoir donner une identité à la nation, d'où
l'obsession du complot et la xénophobie
- les disciples du fascisme sont humiliés par la richesse des ennemis, mais en
même temps, les ennemis sont faibles car les fascistes les vaincront
- la vie est une guerre permanente, donc le pacifisme est une collusion avec
l'ennemi; cependant, un âge d'or et de paix est promis dès lors que l'ennemie
aura été vaincu
- organisation hiérarchique, où à chaque niveau le supérieur méprise ses
subalternes, renforçant le sentiment d'un élitisme de masse
- chacun est éduqué pour devenir un héros, culte de la mort
- machisme
- les individus n'ont pas de droit, mais le peuple aurait une volonté commune,
interprétée par le dirigeant; le peuple devient une fiction théâtrale
- novlangue, appauvrissement de la langue pour limiter la réflexion.
[ Posté le 23 juin 2017 à 12:07 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Livres/reconnaitre_le_fascisme.trackback
Commentaires
Aucun commentaire
Dimanche, 18 juin 2017
Traduction: [ Google | Babelfish ]
Catégories : [ Bière/The London Beer Factory ]

Passion fruit smell, with hints of mango maybe. Contains malted barley and
malted wheat.
The London Beer Factory, London, England. 4.3% alcohol.
[ Posté le 18 juin 2017 à 13:02 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/The_London_Beer_Factory/the_london_beer_factory_beyond_the_pale.trackback
Commentaires
Aucun commentaire
Samedi, 17 juin 2017
Traduction: [ Google | Babelfish ]
Catégories : [ Cuisine/Chocolats ]
Michel Daniel, Brésil 62%: chocolaté?
Michel Daniel, Pérou 64%: légèrement farineux, crème de marrons?
Michel Daniel, Réublique dominicaine 64%: légèrement fruité
Michel Daniel, Haiti 65%: ???
Michel Daniel, Grenade 65%: bonbon, très bon
Michel Daniel, Ghana 68%: frais, fleuri
Michel Daniel, Papouasie 70%: amer, un coté camembert, fumé
Michel Daniel, Équateur 76%: noix de coco, cannelle, très bon
Kultasuklaa, luomu raakasukla 70%: sucre roux, frais
Arctic choc, tummasuklaa 70%: pâteux, grillé
[ Posté le 17 juin 2017 à 14:44 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Cuisine/Chocolats/chocolats_32.trackback
Commentaires
Aucun commentaire
Dimanche, 11 juin 2017
Traduction: [ Google | Babelfish ]
Catégories : [ Bière/Tiny Rebel ]

Flowery, just another ale. Contains malted barley and malted wheat.
Tiny Rebel Brewing Co., Newport, Wales. 4.6% alcohol.
[ Posté le 11 juin 2017 à 14:43 |
pas de
commentaire |
lien permanent ]
Adresse de trackback
https://weber.fi.eu.org/blog/Biere/Tiny_Rebel/tiny_rebel_cwtch.trackback
Commentaires
Aucun commentaire


























© Amazon.fr
Tem est engagé par le président d'une des huit technotrans pour enquêter sur les morts suspectes des membres d'un groupe de musique à la mode. Ces personnes sont connues pour abuser des psychotropes, et leurs morts ne sont pas forcé...