A Better PasswordCard?
Categories: [ IT ]
The PasswordCard sounds like a good idea (and it actually may be in practice), but I don't like it so much for three reasons:
- The entropy is too low (64 bits spread over 232 symbols) and generated from an unknown source of entropy.
- You have to memorize a cryptic symbol and a color for each password, which makes it easy to forget which symbol/color pair is associated with what password.
- I didn't invent it :)
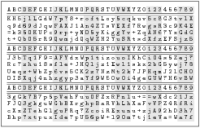
My current idea is to generate a similar card using a hardware random
number generator
so that each symbol on the card has an entropy of 6 bits (2592 bits in total
on he card). I also would like to get rid of the method that consists in
choosng one spot on the card and reading in one direction, and instead use the
card as a lookup table for a substitution cipher: you choose a cleartext
mnemonic for a given website with a length corresponding to the length of the
password you want to generate (e.g., “EXAMPLEC” for an 8-symbol password to
be used on example.com), and you generate the corresponding password by
looking up the symbol corresponding to “E” on the first row of the card,
then the one corresponding to “X” on the second row, “A” on the third,
“M” on the fourth, and so on.
The drawbacks are numerous:
- Reading a password this way is very slow and error-prone (the alternating gray and white areas and the repeated header lines make it only slightly less painful).
- Generating two passwords from the same card is fine as long as the two mnemonics don't share the same characters in the same positions (e.g., “EXAMPLEC” and “EXNIHILO” share “EX” in positions 1 and 2) (if this is the case, the entropy of those particular symbols will be divided by the number of passwords sharing them).
- The mnemonics are meant to be easy to remember, and therefore easy to guess by the thief of the card (that's howerver only slightly worse than the case of the stolen PasswordCard).
- It requires a computer to generate a card that is readable in a small format, so the random bits are temporarily stored on a system that may be compromised (if the physical size of the card does not matter, you can generate such a card by rolling a pair of 6-sided dice about 729 times and writing the symbols down by hand).
There is one benefit though: the card looks very geeky :)
As usual, any comment/idea/criticism is welcome.
[ Posted on August 16th, 2011 at 23:14 | 1 comment | permanent link ]